Blogs
Beyond Monitoring: A Story Every Mid-Market Firm Thinks Won’t Happen to Them
A real-world story of a mid-market firm that passed audits but still missed an attack. Learn how XeneX SOC connects siloed signals, strengthens HIPAA, GLBA, and SOC 2 outcomes, and turns monitoring into real-time threat detection and response.
Why Your SOC Is Losing the Fight — and What Purpose-Built AI Can Do About It
Traditional SOC models can’t keep up with modern threats. Learn why reactive security fails and how purpose-built AI, real-time correlation, and human validation deliver faster, more accurate threat detection and response.
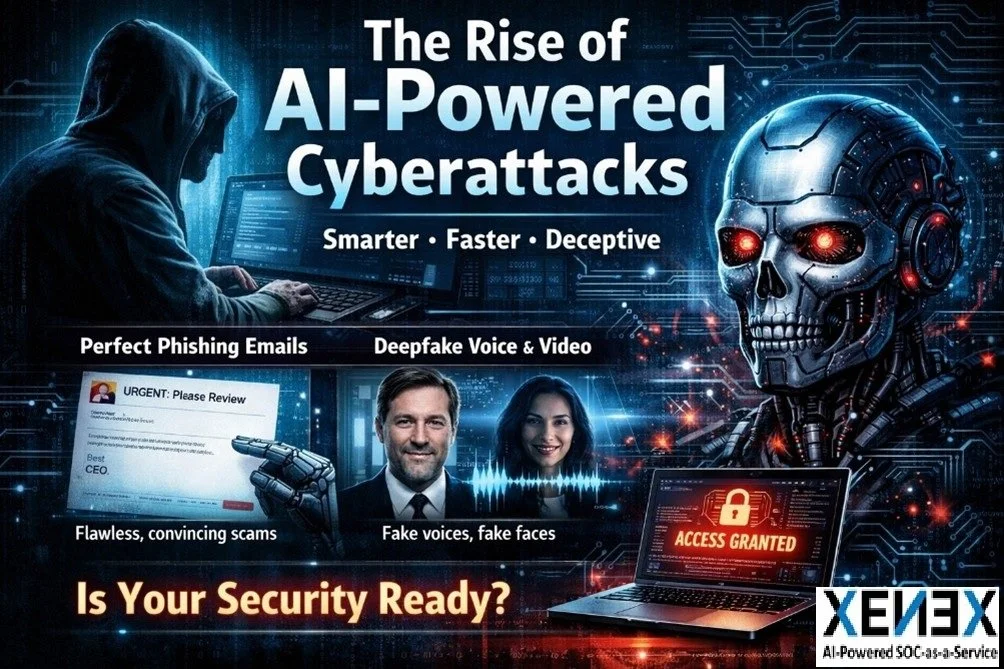
AI-Powered Cyberattacks Are Here. Is Your Organization Ready?
AI-powered cyberattacks are transforming cybersecurity, enabling faster, automated, and more sophisticated threats. Discover how organizations can adapt, strengthen defenses, and stay ahead in this rapidly evolving digital threat landscape.
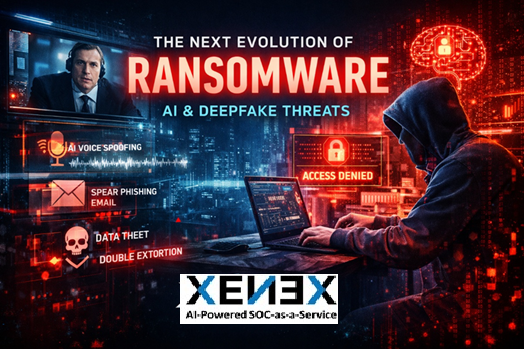
Ransomware Has Changed. Here's What Your Organization Needs to Know.
Ransomware has moved beyond encryption. AI-enhanced phishing, deepfake impersonation, and automated lateral movement are rewriting the threat landscape. XeneX CEO Kevin Nikkhoo breaks down what has changed and what modern defense actually requires.
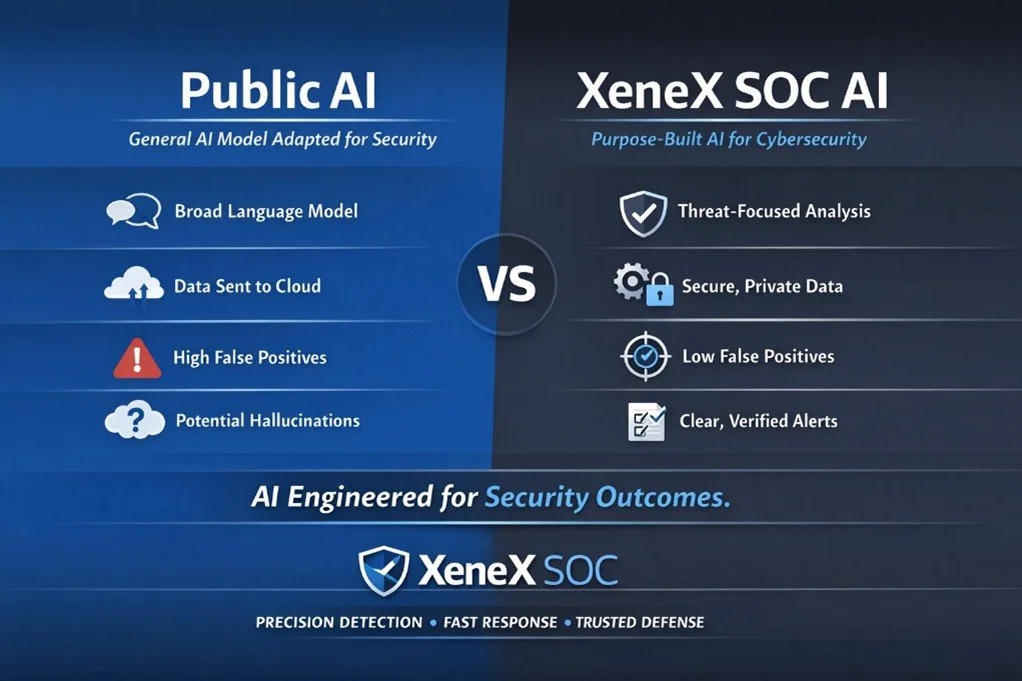
Why Generic AI Fails in Cybersecurity — And What Purpose-Built SOC AI Does Differently
XeneX SOC's purpose-built AI cuts through noise — correlating threats across cloud, endpoints, and identity systems to detect ransomware, credential abuse, and insider risk faster, with fewer false positives and a private architecture that keeps sensitive data protected.
Conduent Data Breach (2025): What Happened, Who Is Affected & How It Could Have Been Prevented
The 2025 Conduent data breach saw the SafePay ransomware group steal 8TB of sensitive data — including SSNs, medical records, and addresses — from a major government services contractor, affecting at least 25 million Americans and ranking among the largest breaches in U.S. history.
Why Is Data Privacy Important for Modern Businesses?
Privacy Requires Continuous Defense -Data privacy cannot be achieved once and assumed permanent. This is the continuous improvement process I advocate, not a one-time project. Threats evolve, systems change, employees transition.
Organizations that combine strong privacy frameworks with proactive SOC monitoring—integrating People, Processes, and Technology—protect sensitive information, meet regulatory obligations, preserve customer trust, and reduce risk.
Why Purpose-Built AI Outperforms Generic AI in Security Operations
Not all AI is created equal in cybersecurity. Learn why purpose-built SOC AI outperforms generic models in threat detection, response speed, privacy protection, and operational trust—and why this architectural decision determines real security outcomes.
The Great List Mix-Up: A Christmas Cyber Caper
When a lonely hacker intercepts Santa's Naughty & Nice List, chaos erupts at the North Pole! Join Santa and the XeneX SOC team as they stop a man-in-the-middle attack and teach about cybersecurity.
What Security Do Healthcare Organizations Need Beyond HIPAA Compliance?
Healthcare security goes beyond HIPAA compliance. Learn what CISOs should watch for in digital and physical environments, what questions to ask SOC providers, and how to protect clinical operations and patient safety.
Cloud & SaaS Security for Manufacturing: Building Trust Across Your Supply Chain
Manufacturing CIOs and CISOs face unique cloud security challenges across regulated environments and supply chains. Learn how XeneX Managed SOC protects intellectual property, supplier data, and compliance through continuous posture management and partnership.
Real BEC Attacks Your Gateway Missed—And How XeneX Builds Trust by Stopping Them
Traditional email gateways miss modern BEC attacks using OAuth hijacks, inbox rules, and VIP impersonation. See real examples and how XeneX's managed SOCaaS protects mailboxes while building client trust.
Protecting K-12 Schools from Ransomware: How XeneX Earns Your Trust
K-12 technology teams face ransomware threats with limited resources. XeneX managed SOC provides 24/7 monitoring, identity protection, and tested recovery plans—building trust through transparent action.
Why NIST-Aligned Security Reports Matter for Enterprise IT Relationships
Trust in cybersecurity requires evidence, not promises. Discover why XeneX's NIST-aligned Security Posture Reports transform SOC partnerships through transparency and accountability both parties can trust.
Concierge Cybersecurity Services Meets AI Defense: How XeneX Delivers Enterprise Value For All
Discover how XeneX redefines cybersecurity by combining dedicated concierge service with proprietary AI-driven technology. Get enterprise-grade threat detection, autonomous remediation, MITRE ATT&CK mapping, and compliance-ready reporting—all designed for organizations that can't gamble on protection.
Are You Happy With Your Cybersecurity Provider?
Most leaders say their cybersecurity is "fine"—until they realize they're drowning in alerts without action. Discover why speed of correlation matters more than detection, and learn the 5 critical questions to ask your provider about automation and response time.
Recent Breaches Proved a Hard Truth: Point Tools Don’t Correlate. XeneX Does.
XeneX AI cybersecurity platform prevents data breaches through real-time kill chain modeling. Autonomous threat detection across cloud, identity, email & endpoints with instant containment actions.
How XeneX SOC Could Have Prevented the Devastating Jaguar Land Rover Cyberattack
Jaguar Land Rover's August 2025 cyberattack shut down global production for 3 weeks. Learn how XeneX SOC's AI-powered monitoring and rapid response could have prevented this costly supply chain attack.
The Cyber Arms Race: Why Your SOC Needs an AI Upgrade
Cyber attacks now move faster than human SOC analysts can respond. Discover how XeneX's AI-powered SOCaaS platform transforms security operations with machine-speed detection and human expertise.
The Cybersecurity Tool Overload Problem — and How XeneX SOC Solves It
Stop cybersecurity tool overload! XeneX SOC consolidates 45+ security tools into one AI-powered platform. Get unified EDR, SIEM, vulnerability management & 24/7 monitoring. Reduce costs, eliminate blind spots & accelerate threat response.